Background
Online businesses connect with their customers over the internet through a device, like a laptop or phone, using a web browser or an app. Having insights into these devices can help a business ensure the person they are interacting with is legitimate. For existing customers, having a list of approved devices can speed someone through the login process, but if a new device is detected, that might be a good time to challenge a login. Also, for new customer sign ups, the device can be looked at for signals that something is amiss.
What is device fingerprinting
Device fingerprinting is a way of identifying the software and hardware of a device in order to distinguish one device from another. Once device information is collected, details are passed through an algorithm that creates and assimilates a unique ID that can be used to recognize the device.
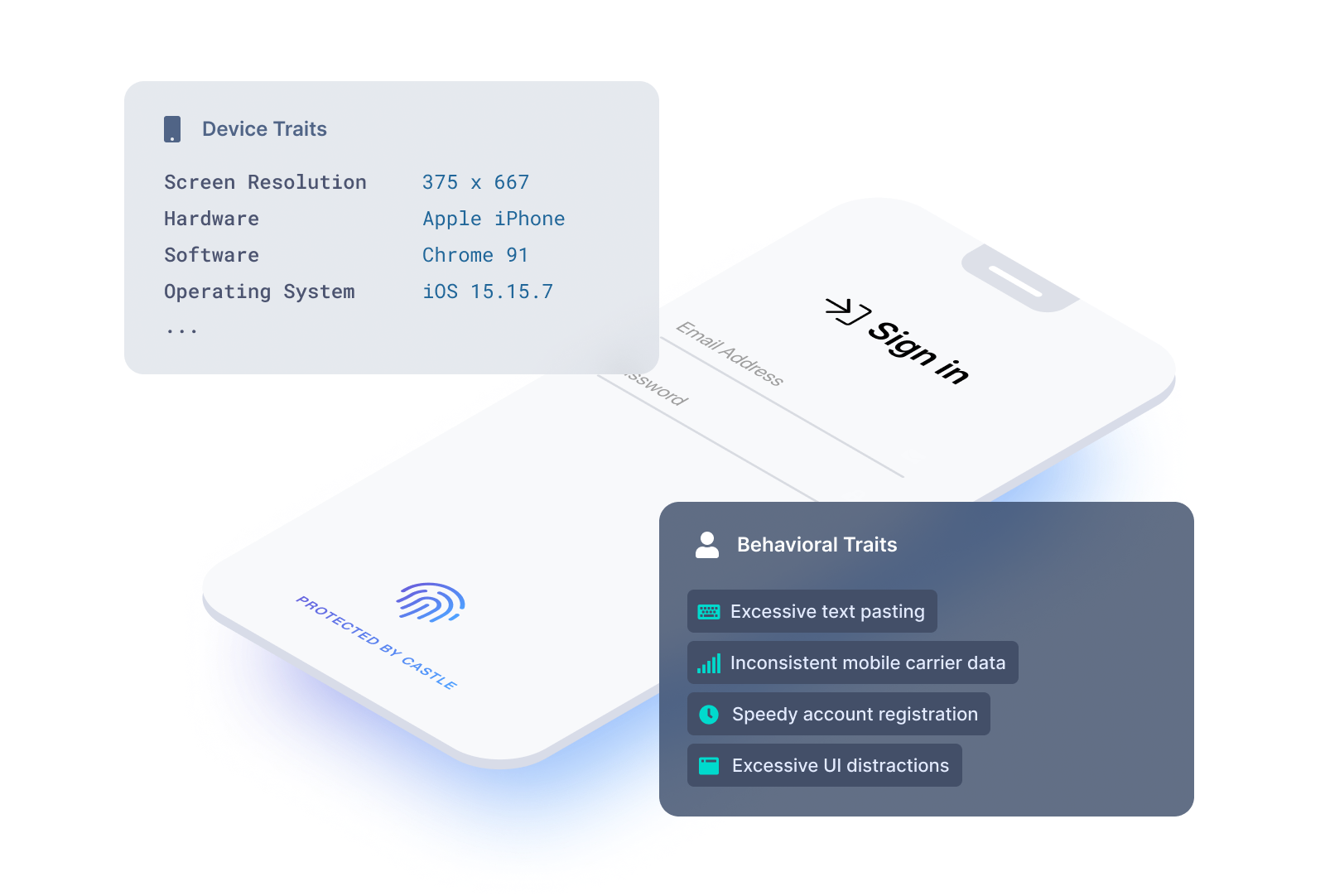
When fingerprinting a device, hundreds of data points are taken into account. Here are some examples of the data that is commonly looked at:
- IP address
- User agent
- HTTP request headers
- Screen size
- Screen resolution
- Device memory
- Installed plugins
- OS
- Time zone
- Language configuration
- Mobile carrier
- Network, bluetooth, and WiFi configuration
- … and many more
Traditional methods of device fingerprinting don’t work
Accurate device fingerprinting is difficult to do. Google, Apple, Firefox and newer browsers such as Brave are increasingly limiting the data that javascript code is able to extract, especially when it's done by third party services looking to track users across websites. By removing, consolidating, or randomizing parameters, the browsers have made it hard to uniquely identify a device by simply looking at standard device characteristics, which is what most device fingerprinting algorithms rely on.
A new way of device fingerprinting
Castle implements device fingerprinting by looking at a wide range of device properties. However, unlike traditional device fingerprinting, Castle's approach also takes into account user behavior. This approach to evaluating behavioral patterns along with device characteristics is what we call "behavioral fingerprinting". Even when the fidelity of device data is relatively low, Castle is still able to identify devices and the users they belong to by looking at behavioral patterns and evaluating the similarities.
For example, if a user accesses a website using an iPhone 8 with iOS version 12.2, then two days later accesses the site with similar device characteristics except for a new iOS version of 12.3, then it’s safe to assume it’s the same device.
Another example is when different users sign up for a service in a short period of time with devices that are almost identical. Using machine learning models, Castle will be able to identify that both users are on the same device. Detecting multiple users on the same device is important to businesses such as financial services where this pattern is often associated with fraudulent activity.
Finally, bad actors will attempt to circumvent device fingerprinting by changing device parameters. This is relatively easy to do manually or by using a browser plugin. However, Castle can detect that a device’s parameters don’t match any real world devices and will flag the device as having been tampered with. A device that’s been tampered with is almost always a sign of a fraudster.
Conclusion
As criminals continue to look for ways around device fingerprinting, and browsers continue to increase user privacy by actively preventing fingerprinting, Castle's unique approach offers a future-proof and dynamic approach to this challenging problem.
If you want to try our device fingerprinting for yourself, sign up for a free trial of Castle at castle.io.







